What’s the difference between passwords and passkeys? It’s not just the protection they provide
- Written by The Conversation
Passwords are the keys to our digital lives – think how many times you log in to websites and other systems. But just like physical keys, they can be lost, duplicated and stolen.
Many alternatives have been proposed in recent years, including passkeys. These offer a significant improvement in terms of user friendliness and potential for widespread use.
But what exactly are they – and how do they differ from passwords?
Passwords are vulnerable
In simple terms, a password is a secret word or phrase that you use to prove who you are to computer systems and/or online. If you have an account on a website or subscribe to a service provider you likely have many.
Passwords themselves are fine; it is the way we implement and use them that makes them vulnerable. For example, weak password habits are everywhere. A CyberNews report from earlier this year identified 94% of 19 billion leaked password were re-used. It also identified several similarities in passwords, including strings of numbers such as “123456”, people’s names, cities, popular brands and swear words.
And when a breach occurs, stolen passwords can spread quickly. This leads to accounts being taken over, identity theft and/or phishing attacks. In one experiment, hackers were trying to use leaked credentials within an hour.
Passwords are also vulnerable to phishing, which is when scammers trick you into typing your password (or other information) into a fake account login page. Phishing emails continue to grow in number and consequence with one report indicating more than 3 billion phishing emails sent per day globally.
A good password is unique (that is, never re-used) and complex (imagine a sequence of letters, numbers and symbols such as “e8bh!kXVhccACAP$48yb”). It can also be a unique combination of multiple words to create a phrase or memorable sequence.
This could be difficult to remember, although creating a story that uses the contents of the password might help. For example, say your password was “CrocApplePurseBike”. You could remember it by thinking of the Crocodile that packed its Apple into a Purse before riding a Bike.
What are passkeys and how do they work?
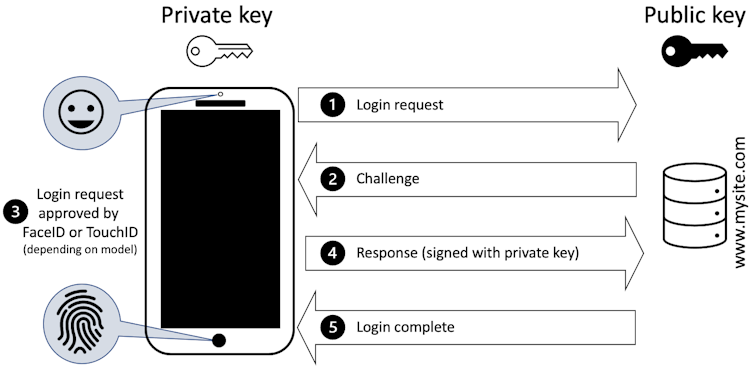
Passkeys first started to emerge roughly four years ago. They use a mathematical process called public-key cryptography to create a unique set of information that is split into two parts – or keys.
One key is public and can be shared with websites; the other is a private key that is stored securely on your device. To sign into an account, the website sends a random challenge (such as a number) and your device uses the private key to “approve” the login request. This approval is usually called “signing” the request and applies a mathematical process to the challenge.
Your device won’t just do this automatically; you will typically be required to approve the request. For many mobile devices this will require your face or fingerprint to be used to authorise the response to be sent.
Finally, the website checks the signature via the public key it already has. If it confirms the challenge, you are in.
Stronger by design
Passkeys are stronger than passwords by design. It doesn’t matter if the public key is stolen, because it cannot be used on its own. Your private keys are safely protected by your device’s security, with most using face or finger-based biometrics to unlock (it is best to avoid relying on a PIN).
Each passkey is also unique for every service you use; even if the key for a site could be stolen, it cannot be used elsewhere.
Another plus is that passkeys are resistant to phishing. From a user perspective, there isn’t a password to send in response to a phishing email. A request to log in on a site has to come from the registered device combined with the approval of the user.
Passkeys are also more convenient than passwords. You don’t have to look for the password you used when you registered – the passkeys are already linked to your device and are only a finger/face verification away.
There are, however, some issues with passkeys. For one, while many browsers, operating systems and websites are embracing passkeys, this isn’t universal. And some early implementations suffered with compatibility between devices (such as between Microsoft and Apple devices).
As users move to newer devices and manufacturers improve integration, these issues should disappear.
A clear winner
From a security point of view, passkeys are the clear winner. They offer stronger protection, can resist phishing and are easier to use. But until passkeys are everywhere, passwords will still play a supporting role.
Implementing passkeys on a website requires effort from the company concerned. With a vast number of sites requiring users to create accounts, the process of migrating them all to passkeys is going to take decades. Many will never adopt the practice unless other factors force their hand.
For now, it’s crucial that we continue to focus on password hygiene by using strong, unique passwords and enabling multi factor authentication wherever possible. If you do nothing else after reading this article, at least change any re-used passwords.